Nmap In The Movies
For reasons unknown, Hollywood has decided that Nmap is the tool to show whenever hacking scenes are needed. At least it is a lot more realistic than silly 3D animation approach used in many previous movies (e.g. "hacking the Gibson" on Hackers, or the much worse portrayals on Swordfish). We always like to see Nmap in the movies, so we have catalogued known instances here.
If you catch Nmap in another flick, please mail Fyodor.
Update (April 21, 2020): I (Fyodor) am way behind on adding new movies. Sorry about that!
Movie script writers, artists, and digital asset managers are also welcome to email Fyodor for advice. We've been pleased to help out to make a number of movies slightly more realistic and entertaining by improving the hacking scenes.
This page only covers movies, we have a separate page coving news articles, reviews, books, and popular culture references.
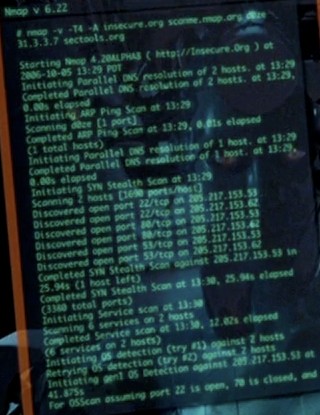
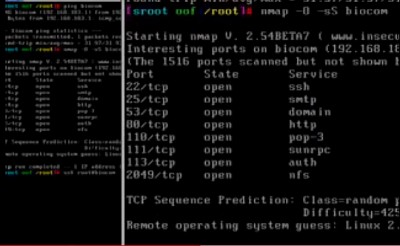
Matrix Reloaded
While Nmap had been used in some previous obscure movies, it was The Matrix Reloaded (Wikipedia, IMDB, Amazon) which really turned Nmap into a movie star!
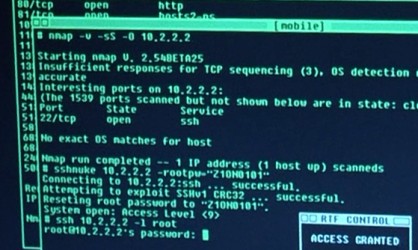
We have all seen many movies like Hackers which pass off ridiculous 3D animated eye-candy scenes as hacking. So Fyodor was shocked to find that Trinity does it properly in The Matrix Reloaded. Needing to hack the city power grid, she whips out Nmap version 2.54BETA25, uses it to find a vulnerable SSH server, and then proceeds to exploit it using the SSH1 CRC32 exploit from 2001. Shame on the city for being vulnerable (timing notes).
A video of the exploit is available on YouTube or as matrix-nmap.mp4. Click on the following thumbnails for higher resolution or view more pictures here.
Updates:
- News articles about the Matrix cameo: BBC, Slashdot, SecurityFocus, Silicon.Com
- JWZ has added this cracking scene as an XScreenSaver 4.10 Easter Egg - run 'xmatrix -small -crack'.
- Several people have submitted matrix-themed banners to the propaganda gallery. Feel free to use any of these to link to Insecure.org - we appreciate it!
- The UK's Scotland Yard Computer Crime Unit and the British Computer Society have put out a joint warning that "Viewers of the new box office blockbuster 'Matrix Reloaded' should not be tempted to emulate the realistic depiction of computer hacking." Kids - don't try this at home!
Ocean's 8
Ocean's 8 (Wikipedia, IMDB, Amazon) is a 2018 comedy heist film starring Sandra Bullock, Rihanna, Cate Blanchett, and Anne Hathaway that continues the series started by Ocean's Eleven in 2001. Rihanna plays the film's main hacker, Nine Ball. She uses Nmap in many scenes to compromise people and companies responsible for guarding the $150 million diamond necklace they want to steal. Nmap is normally shown in the background as context to her hacks rather than taking the leading role.
In this screen (full version), Nmap is shown in the two screens on the right while they are 3D-scanning their target necklace on the left:
And here is the whole gang gathered together to (presumably) analyze their Nmap results (image is from The Mercury News):
Even the movie trailer has a glimpse of Nmap at 1:50:
For more details on the Ocean's 8 hacking scenes themselves, see security researcher Samy Kamkar's analysis.
Congratulations to Alejandro Hernandez for being first to discover and report the Nmap scenes!
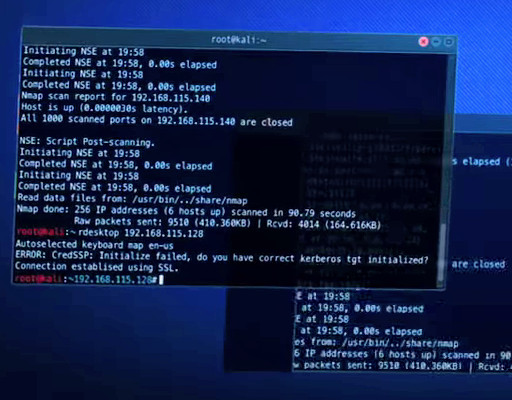
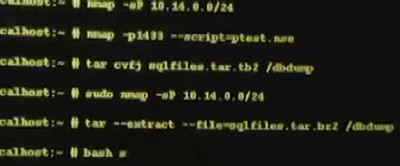
Snowden
Oliver Stone's 2016 Snowden film (Wikipedia, IMDB, Amazon) dramatizes Edward Snowden's massive leak of classified documents revealing NSA widespread surveillance of U.S. citizens. In one early scene, Snowden is given a network security challenge at a CIA training class which is expected to take 5 to 8 hours. But with the help Nmap and a custom Nmap NSE script named ptest.nse, Snowden stuns the professor by completing everything in 38 minutes! Nmap's distinct tabular output is visible on other students' screens too, though we may have to wait for the 4K resolution film release to read the exact text. Here are a couple screen shots from the Nmap scenes:
And here is the whole trailer (with Nmap glimpse at 34 seconds in):
Congratulations to Prabesh Thapa from Nepal for being first to discover and report the Nmap scenes!
Dredd
Dredd (Wikipedia, IMDB, Amazon), a film adaptation of the famous Judge Dredd comics, was released in 2012 and contains multiple Nmap scenes.
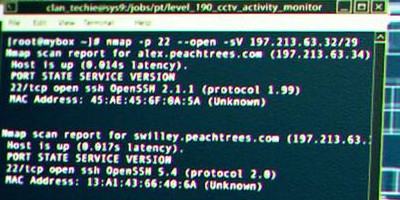
In the vast, post-apocalyptic metropolis of Mega City One, the only law is provided by the Judges of the Hall of Justice—cops with the power of judge, jury and executioner. Most feared among these law-keepers is the ruthless and implacable Judge Dredd (Karl Urban). He and Cadet Judge Cassandra Anderson (Olivia Thirlby) infiltrate a notorious high-rise slum tower controlled by former prostitute-turned-drug-lord Ma-Ma (Lena Headey). For network reconnaissance and exploitation of the slum tower network, they turn to Nmap! The three minute movie trailer briefly shows an Nmap version scan against TCP port 22 (SSH):
Congratulations to Aleksei Usov for being first to discover and report the Nmap scenes!
Elysium
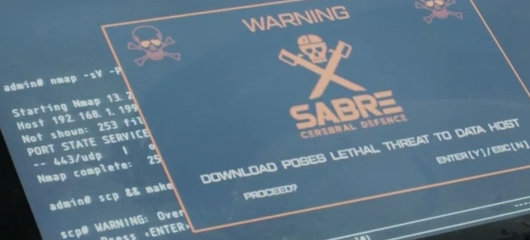
The 2013 science-fiction film Elysium (Wikipedia, IMDB, Amazon) stars Matt Damon and Jodie Foster. It takes us to the year 2154 when an overpopulated Earth teems with poverty, crime, and destruction while the rich live on a luxurious space station. Nmap version 13 (I guess this really is the future!) is used to port scan Matt Damon's augmented brain before transferring the data he carries in an attempt to hack the space station.
Nmap action:
Trailer:
Congratulations to Tavis Ormandy and André Luna for discovering the Nmap scenes first.
Fantastic Four
Fantastic Four (Wikipedia, IMDB, Amazon) is a 2015 big-budget superhero film based on the Marvel Comics team of the same name. In the film, Sue Storm (played by Kate Mara) uses her Nmap skills to track down a companion. Her computer flashes "IPSCAN", then "TRACEROUTE", "PORTSCAN", and finally "NMAP". Screen shots (click the 2nd one to see the wider shot):
Trailer:
Congratulations to grmlber for being the first to notice and report it!
Who Am I—No System Is Safe
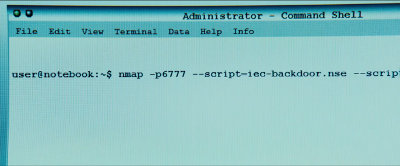
Who Am I—No System is Safe (Wikipedia, IMDB, Amazon) is a 2014 German cyber-thriller about dueling hacker groups (patterned after Anonymous) vying to commit the most audacious system compromises and pranks. During an initiation scene 13:40 into the movie, the protagonist Benjamin proves his skills by compromising the local power company and causing a brief blackout. He does so by running an Nmap Scripting Engine (NSE) script that he has presumably written. The script is named iec-backdoor.nse, referencing the International Electrotechnical Commission (IEC) standards which control utility power grid equipment. This bit of realism is a nice touch! Screen shots:
Trailer:
Congratulations to Edko for being the first to notice and report it, and Thomas Zuber for sending the first screenshot!
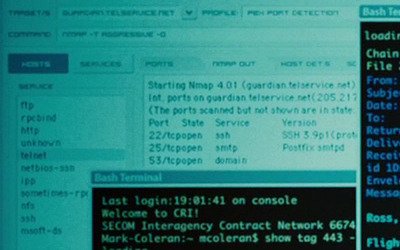
Bourne Ultimatum
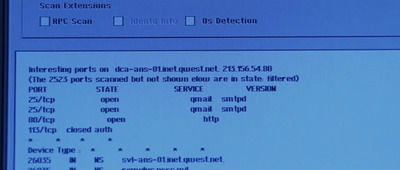
In The Bourne Ultimatum (Wikipedia, IMDB, Amazon), the CIA needs to hack the mail server of a newspaper (The Guardian UK) to read the email of a reporter they assassinated. So they turn to Nmap and its new official GUI Zenmap to hack the mail server! Nmap reports that the mail server is running SSH 3.9p1, Posfix smtpd, and a name server (presumably bind). They also make substantial use of Bash, the Bourne-again shell. Congratulations to Roger Chui for being the first to spot this. He also sent a scene transcript and the following HD screen shots (click for full resolution):
Die Hard 4
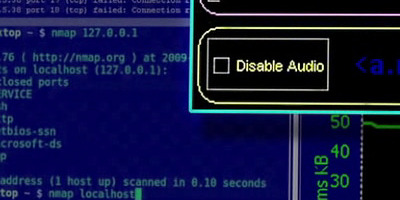
Yippee Ki-Yay! In Die Hard 4: Live Free or Die Hard (Wikipedia, IMDB, Amazon), Detective John McClane (Bruce Willis) is dispatched to retrieve hacker Matthew Farrell (Justin Long) because the FBI suspects him of breaching their computer systems. Later, Justin is enlisted to help thwart terrorist mastermind Thomas Gabrial's attempts at total World destruction. In this Scene, Farrell demonstrates his Nmap skills:
Thanks to Andrew Hake for catching the cameo and sending these HD screen shots.The scene occurs about 8 minutes into the movie.
The Girl with the Dragon Tattoo
The Girl with the Dragon Tattoo (Swedish: Män som hatar kvinnor) is a 2009 Swedish thriller film (Wikipedia, IMDB, Amazon) based on the Internationally bestselling novel by Stieg Larsson. It follows Lisbeth, a troubled young hacker suffering from Asperger syndrome and a history of abuse by authority figures, as she works with a journalist trying to solve a 40-year old murder mystery. It was the third-highest grossing non-English film of 2009.
The Nmap scene lasts only moments and occurs about 6 minutes in. Note that this is the original film (English subtitled version available on Amazon). A big-budget Hollywood remake was released in 2011 (IMDB, Wikipedia, Amazon), though they may have ruined it by cutting the Nmap scene!
Trailer for the 2010 US/UK subtitled release:
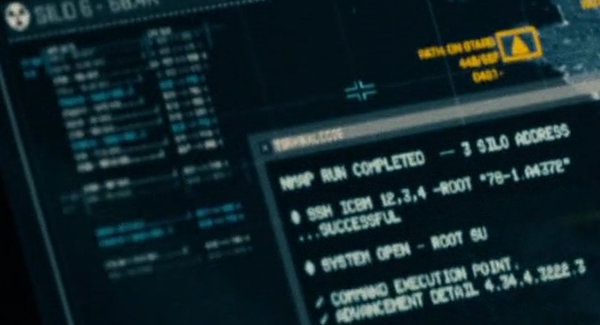
G.I. Joe: Retaliation
Nmap is used to launch nuclear weapons in the 2013 action film G.I. Joe: Retaliation (Wikipedia, IMDB, Amazon). While their syntax is a little screwy, they seem to scan a missile silo with Nmap, ssh to each located ICBM, su to root and then execute commands to arm and launch it. Here are screen shots followed by the movie trailer:
Thanks to Dillon Korman for catching the scene and sending screenshots!
The Listening
Nmap and NmapFE were used in The Listening (Wikipedia, IMDB, Amazon), a 2006 movie about a former NSA officer who defects and mounts a clandestine counter-listening station high in the Italian alps. Thanks to Addy Yeow Chin Heng for the screenshots.
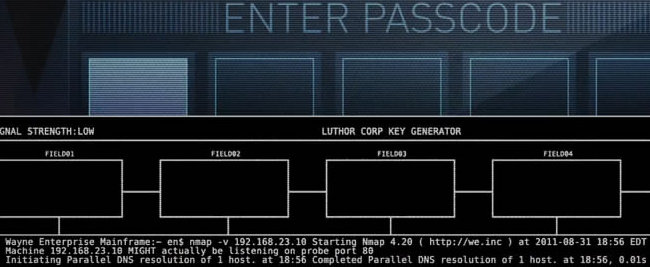
Justice League: Doom
Nmap is used in the opening credits of Justice League: Doom (Wikipedia, IMDB, Amazon). This 2012 animated superhero film features Batman, Superman, Wonder Woman, and Green Lantern battling a team of supervillains. Thanks to Spencer Davenport for catching this and sending screenshots. It is interesting that in most cases (but not all), they changed the Nmap URL (http://nmap.org) in the Nmap output to http://we.inc (Wayne Enterprises). Also, they ran the command in August 2011 using a version of Nmap (4.20) from 2006. I realize that Batman has a lot of important and heroic work to do, but surely he can spare 5 minutes to download and install the latest version of Nmap!
Abduction
Abduction (Wikipedia, IMDB, Amazon) is a 2011 thriller about a teenager (Taylor Lautner from the Twilight series) who sets out to uncover the truth about his life after finding his baby photo on a missing persons website. In the process he is chased by, among other villians, an Nmap-using Serbian hacker henchman. If you notice something familiar about the background Nmap scans in the screenshots below, it's because the film makers directly cribbed some of them from The Matrix Reloaded.
Extracted
The 2012 science fiction thriller Extracted (IMDB, Amazon) portrays a scientist who invents a technique to watch people's memories, but finds trouble when entering the mind of a heroin addict suspected of murder. Nmap is used as part of the system for entering someone's mind (maybe that is an NSE script). Screen shot (click for the whole thing):
A trailer is also available here. Thanks to Sander Ferdinand for discovering and reporting the Nmap scene.
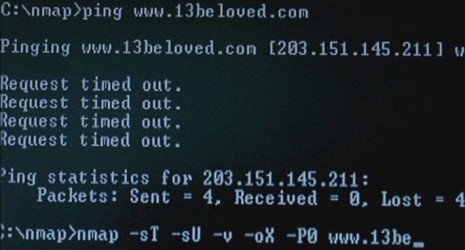
13: Game of Death
Nmap was used in the acclaimed Thai thriller 13: Game of Death (Wikipedia, IMDB, Amazon), also known as "13 Beloved" and "13 game sayawng". This movie follows the story of a man given the chance to complete 13 challenges to win $100,000,000. Successive challenges become increasingly intense, dangerous, illegal, degrading, and grotesque. What would you do for $100 million? Eventually one of his sysadmin friends gets worried about him and she demonstrates Nmap hacking skills by breaking into the twisted game's website (longer summary).
We have received an AVI video (5MB) of the scene, and also numerous screenshots.
Thanks to Tazman for first notifying me of the scene, and to Laga Mahesa and Ithilgore for sending screenshots.
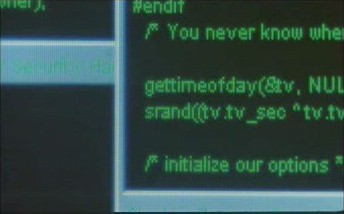
Battle Royale
Battle Royale (Wikipedia, IMDB, Amazon), also known as Batoru Rowaiaru, is a bizarre and controversial Japanese movie about a class of 9th graders sent by the government to an abandoned island to be fitted with explosive collars and forced to kill each as part of a twisted survival game. One of the students is a hacker, and can be seen referencing Nmap source code in these clips:
Broken Saints
Broken Saints (Wikipedia, IMDB, Amazon) is an award-winning animated film series (motion comic) produced in 24 chapters first published online between 2001 and 2003. It was then improved for the 2006 DVD release distributed by 20th Century Fox. It is a complex, 12-hour tale of four strangers from "the quiet corners of the globe" connected by a vision they all receive of coming evil.
One of those four strangers, Raimi, is a young security software developer who uses Nmap to compromise systems and uncover corporate treachery at his estranged employer. The Nmap Scene is in Chapter 2, Cryptic, and can be viewed free on Youtube. You don't really need to watch Chapter 1 first, but it is available here. The Nmap cameo was first discovered by David Alexander. Screenshots:
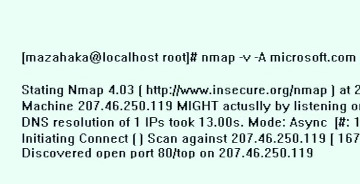
Khottabych
Nmap (and then telnet) are used by a teenage hacker (Gena) to deface Microsoft.Com in the 2006 Russian film Khottabych (Wikipedia, IMDB). Microsoft and the US authorities are understandably upset by the attack, so they send the attractive female hacker Annie to flush him out. The movie also features an epic battle between powerful genies (the kind which come in a bottle) fighting for dominion over Earth. Thanks to Paul Shatov for notifying us and sending the screenshots! I bought this DVD from Amazon, but it is region 5 and offers no English dubbing or subtitles. I had to use this subtitle file. Wikipedia claims that a region 1 English DVD was released.
HaXXXor: No Longer Floppy
With the risque "HaXXXor" series of low-budget films, Nmap makes the leap from Science fiction to soft-core pornography. “HaXXXor Volume 1: No Longer Floppy” includes a lengthy Nmap training scene by model E-Lita. Here are some photos from early in the scene while she is still clothed:
Bloody Monday
In the Japanese drama series Bloody Monday, a hacker named Falcon must use his computer skills to unravel a mysterious project “Bloody Monday” and prevent a biological terrorist attack from devastating Tokyo. Nmap is used in multiple episodes, starting with Season One, Episode One. You can also find Nmap used about 20 seconds into this clip (Season 2, Episode 4). Other security tools portrayed realistically include Netcat, Rainbow Crack, and an Sadmind exploit. Thanks to Shirase Akira for reporting this first.